Alerts to Improve Network Visibility
Alerting Made Easy
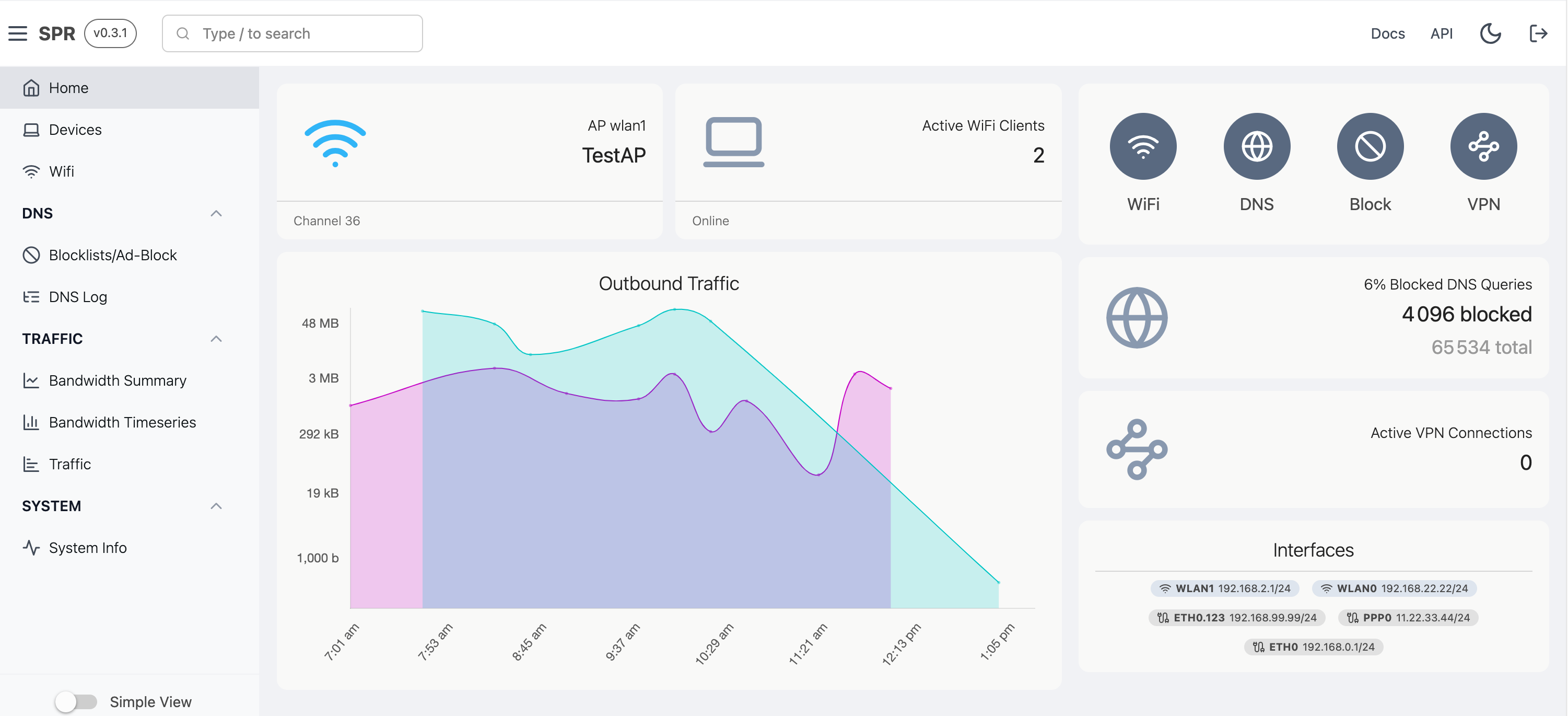
We've rolled out a lightweight alerting mechanism built right inside of SPR.
So SPR already has an event system and we wanted to improve the existing notification system as well as persist alerts for later.
We wanted something with the following properties:
- Allow powerful matching expressions
- Work with our lightweight key-value database for concurrent access
- Minimal system performance impact
- User Customizable, in UX with minimal coding