SPR Is Immune to MACStealer (CVE-2022-47522)
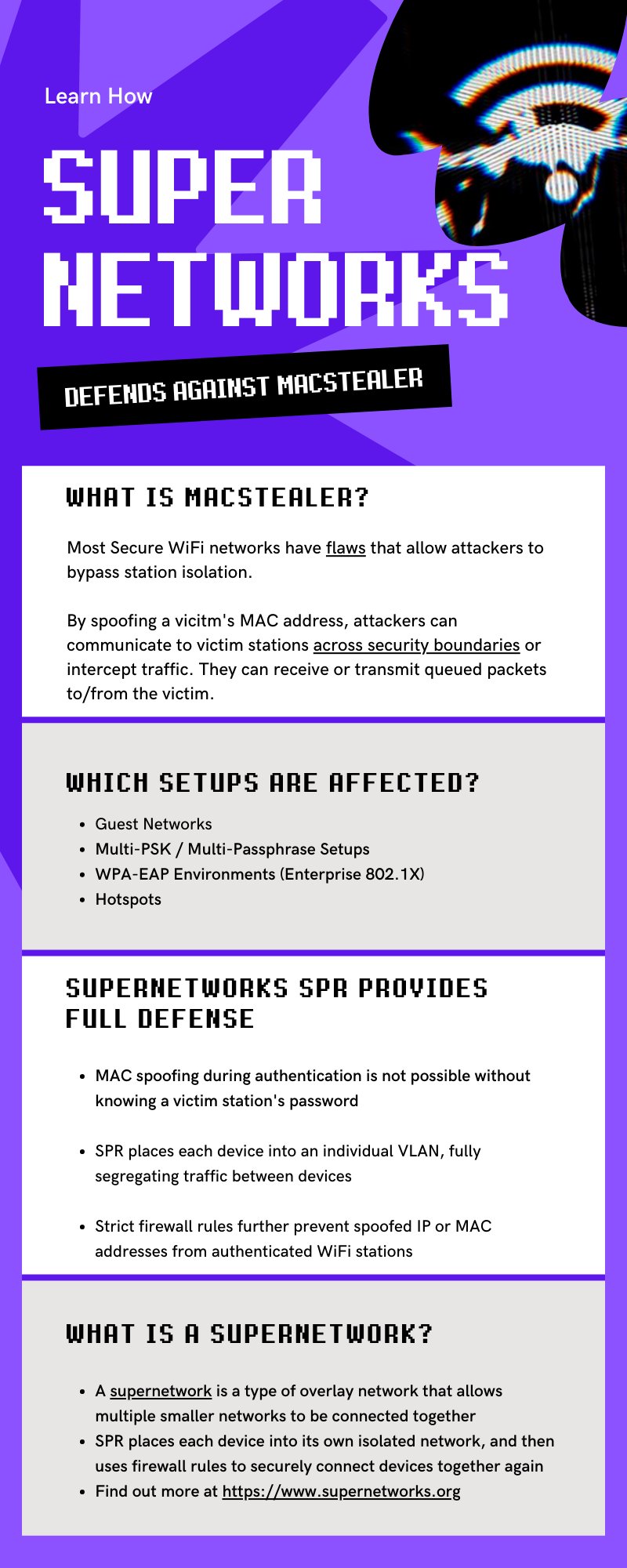
The MACStealer attack (CVE-2022-47522) published by Mathy Vanhoef demonstrates how attackers can bypass WiFi client isolation by spoofing a victim's MAC address. By doing so, they can intercept queued frames or communicate across security boundaries on the same access point.
Guest networks, multi-PSK setups, WPA-EAP environments, and hotspots are all affected.
SPR is immune to this category of attack for three reasons:
- MAC spoofing during authentication is not possible without knowing the victim's unique password. Every device on SPR has its own WiFi credential — there is no shared password to compromise.
- Each device is placed into its own VLAN. There is no shared broadcast domain for an attacker to pivot within.
- Strict firewall rules block spoofed IP and MAC addresses from authenticated WiFi stations, providing defense in depth beyond VLAN isolation alone.
MACStealer bypasses ap_isolate and similar firmware-level client isolation because those mechanisms have state errors in low-level MAC address handling. SPR's per-device VLAN architecture operates above that layer entirely — the firmware isolation bugs are irrelevant when there are no co-located clients to attack.
For more details see the MACStealer repository and our knowledgebase article.